Melody J. Kaufman, cyber security specialist at Saviynt gives us a take probing the recent state of the white-collar twitter attacks and state of security
After all of us heard the recent news about the Twitter attacks, it not only sent us to a frenzy of shock but was also the much needed wake-up call for the online fraud that goes on. It made us put forth certain prominent questions on Risk management, online security and compliance.
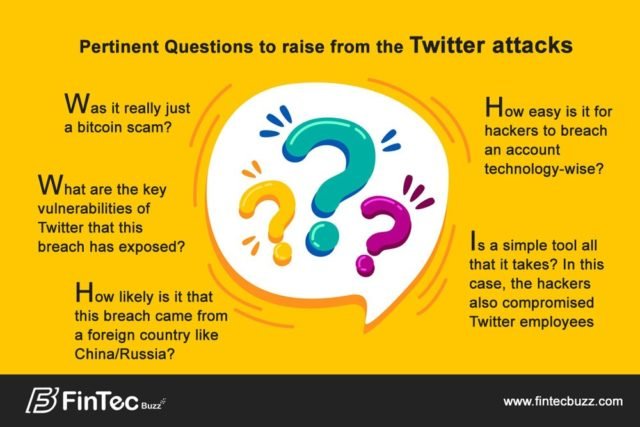
What were the hackers ultimate goal? Was it really just a bitcoin scam? What are the key vulnerabilities of Twitter that this breach has exposed? How likely is it that this breach came from a foreign country like China/Russia? – How easy is it for hackers to breach an account technology-wise? Is a simple tool all that it takes? In this case, the hackers also compromised Twitter employees. What are the biggest takeaways from this hack?
Was it really just a bitcoin scam?
I don’t think this was entirely a bitcoin scam but instead a proof of concept in which bitcoins were just a side venture. I think the ultimate goal was to prove that high profile accounts are vulnerable and can be subverted to message on behalf of others. The bitcoin angle serves as a good cover for real motive as it seems to the onlooker that the attackers have gotten what they wanted.
What were the hackers ultimate goal?
There are many reasons hackers would want to compromise high-profile social media accounts. Influence has become a form of currency with which a lot of things can be bought. Given that we’ve already seen the way social media can be used to influence popular opinion and given that this is an election year. It seems to me that once you have a proof-of-concept that these verified accounts can be hacked there are two easy logical leaps. One is to damage the credibility of Twitter’s system which allows the shadow of doubt to be cast on legitimate statements by high-profile individuals. The other possibility is to potentially compromise such accounts in the future and disseminate altered messaging in more subtle ways to leverage their influence to impact state and national issues.
What are the key vulnerabilities of Twitter that this breach has exposed?
The key vulnerabilities of Twitter that were exposed come down to challenges in trusting internal users and validating identities of external parties. From what we are seeing, the attack was either initiated through an internal user or using their credentials. If this administrative system that allows access to these high profile accounts was more tightly secured with better controls such as a second user signoff on tasks related to “verified” users, much the way many accounting systems operate, this attack would either have been stopped early or blocked altogether.
How likely is it that this breach came from a foreign country like China/Russia?
Whether this breach originated in China or Russia is moot outside of motivation as it is trivial for the IP of origin to appear from any country the attacker wishes. Either way, I am quite confident that the attack was not trivial in terms of execution. I think it was a complex combination of social engineering and compromising some asset either via rootkit or theft. I anticipate this is not their end goal but rather a test run and other compromised accounts/users exist.
In this case, the hackers also compromised Twitter employees. What are the biggest takeaways from this hack?
The biggest takeaways from this hack are for users of Twitter to not trust that messaging from “verified” accounts is legitimate. Assume that there is a risk of compromise and do not think that direct quotes on here are 100% indicative of the actual user tweeting, especially if they happen to be a world leader.
For Twitter, this hack is indicative of some major security failures on multiple fronts. First off, there are too many individuals that have access to administrative tools. Second, they need to include controls to ensure that no single individual can alter trusted/verified accounts without a significant level of oversight. In addition, Twitter needs to improve the tracking of logs for this administrative interface with some user behavioral analytics. Look for trends such as a support person taking administrative actions on a greater percentage of verified accounts relative to their peers. This simple step alone would have flagged that a user was compromised early on in the attack.

Melody J. Kaufman
Melody J. Kaufman, cyber security specialist at Saviynt. She has Over 20 years of diverse technology experience including designing, developing, and implementing applications, systems, and enterprise-level solutions that improve organizational agility.